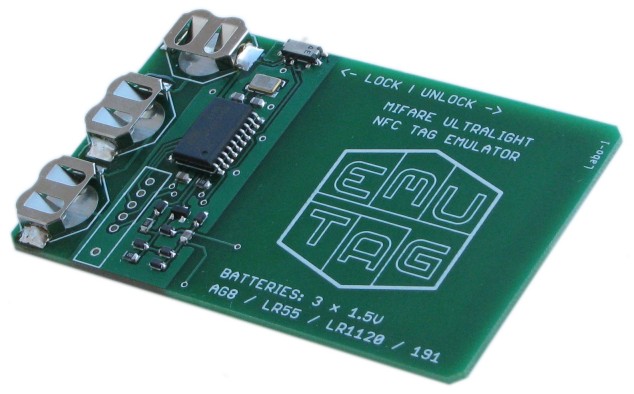
Introducing a Portable Standalone MIFARE Ultralight and NTAG2x3 Emulator
Emutag is the easiest to use NFC tag emulator on the market - knowledge of programming languages is not required!
With a flip of a switch, the Emulator is turned from a functional clone [of NFC tag] into a fully writable memory array.
Emulator Overview
This Emulator has been designed to emulate NFC Forum Type 2 tags (ISO 14443 type "A" modulation) with EEPROM memory up to 192 bytes long.
The current firmware releases can emulate the following NFC tags:
- MF0ICU1 MIFARE Ultralight
- MF0UL1101D MIFARE Ultralight EV1 (20 pages)
- MF0UL2101D MIFARE Ultralight EV1 (41 pages)
- NT2H0301 NTAG203
- NT2H1311 NTAG213
In addition to replicating the wireless interface of tags, their memory architecture, and internal state machine, the Emulator offers features of programming a custom UID, manufacturer byte, internal data byte, as well as resetting OTP bits, lock and block-locking bits to their initial state of logic 0. All one-way counters of NTAG2x3 and EV1 can be programmed with any value at any time. NTAG213 and EV1 firmware also offers reading out the stored authentication password and ackowledge fields which are write-only on original tags, as well as instantly removing read and write protection imposed by PROT and AUTH0 fields. The new Password Sniffer Mode introduced in 2017 allows storing the password from AUTHENTICATE command argument. The 32-byte signature of NTAG213 and EV1 can be programmed by a series of 8 writes to 8 pages in a single NFC session. All this makes the Emulator ideal for software development, system testing, and application support, in cases where project development or system administration require many test-case scenarios involving memory areas with security restrictions.
What the Emulator is:
- Swiss-army knife in application-layer development and debugging MIFARE Ultralight and NTAG2x3 based systems.
- Replacement for tens and hundreds of standard NFC tags wasted in system testing involving lock bits and one-way counters.
- According to RFID device classification, it is inside 13.56 MHz proximity device family, inside ISO 14443-A standard including the anticollision routines (part 3 of ISO 14443-A), but outside of smartcard communication specifications (part 4) where APDU commands are involved.
- It could be used to test NFC readers for functionality, but since the Emulator exceeds wireless performance of standard MIFARE Ultralight and NTAG2x3 NFC tags, it is still recommended to test with standard tags.
What the Emulator is NOT:
It is not a signal sniffer of NFC protocols.SDK can now convert it into a downstream-only sniffer.- It is not a reader (PCD) device.
It is not meant for low-level protocol debugging, such as parity bit, CRC, ATQA, and SAK manipulation.SDK can now allow receiving and sending any kind of data.- It does not operate with type B (ISO 14443-B) modulation, similarly to standard type A tags.
- It is not a ISO 14443 part 4 smartcard, so does not work with APDU nor returns an answer to select (ATS).
- It is not an emulator of 125 kHz tags (HID, IOProx, EM4xxx, etc.) mainly used for access control with Wiegand interface devices.
- It is not an emulator of MIFARE Classic NFC tags.
- It is not an emulator of MIFARE Ultralight C
and EV1type NFC tags. EV1 emulation is a new feature since 2017!




